The goal of this guide is to install LibreNMS on an Ubuntu Server with a self signed certificate. Most of the steps are copied out of the LibreNMS Documentation found here.
Install required packages
sudo apt install apache2 composer fping git graphviz imagemagick libapache2-mod-php7.0 mariadb-client mariadb-server mtr-tiny nmap php7.0-cli php7.0-curl php7.0-gd php7.0-json php7.0-mcrypt php7.0-mysql php7.0-snmp php7.0-xml php7.0-zip python-memcache python-mysqldb rrdtool snmp snmpd whois
Create LibreNMS user
sudo useradd librenms -d /opt/librenms -M -r
sudo usermod -a -G librenms www-data
Install LibreNMS
cd /opt
sudo git clone https://github.com/librenms/librenms.git librenms
Configure MySQL
sudo systemctl restart mysql
sudo mysql -uroot -p
Run the following MySQL commands to create the LibreNMS user. Change password to your own password.
CREATE DATABASE librenms CHARACTER SET utf8 COLLATE utf8_unicode_ci;
CREATE USER 'librenms'@'localhost' IDENTIFIED BY 'password';
GRANT ALL PRIVILEGES ON librenms.* TO 'librenms'@'localhost';
FLUSH PRIVILEGES;
exit
Edit following file
sudo vi /etc/mysql/mariadb.conf.d/50-server.cnf
Add the following inside the [mysqld] section
innodb_file_per_table=1
sql-mode=""
lower_case_table_names=0
Restart MySQL
sudo systemctl restart mysql
Configure PHP
Edit the two files and set the time zone, date.timezone. Example “America/New_York”
sudo vi /etc/php/7.0/apache2/php.ini
sudo vi /etc/php/7.0/cli/php.ini
Then run these commands
sudo a2enmod php7.0
sudo a2dismod mpm_event
sudo a2enmod mpm_prefork
sudo phpenmod mcrypt
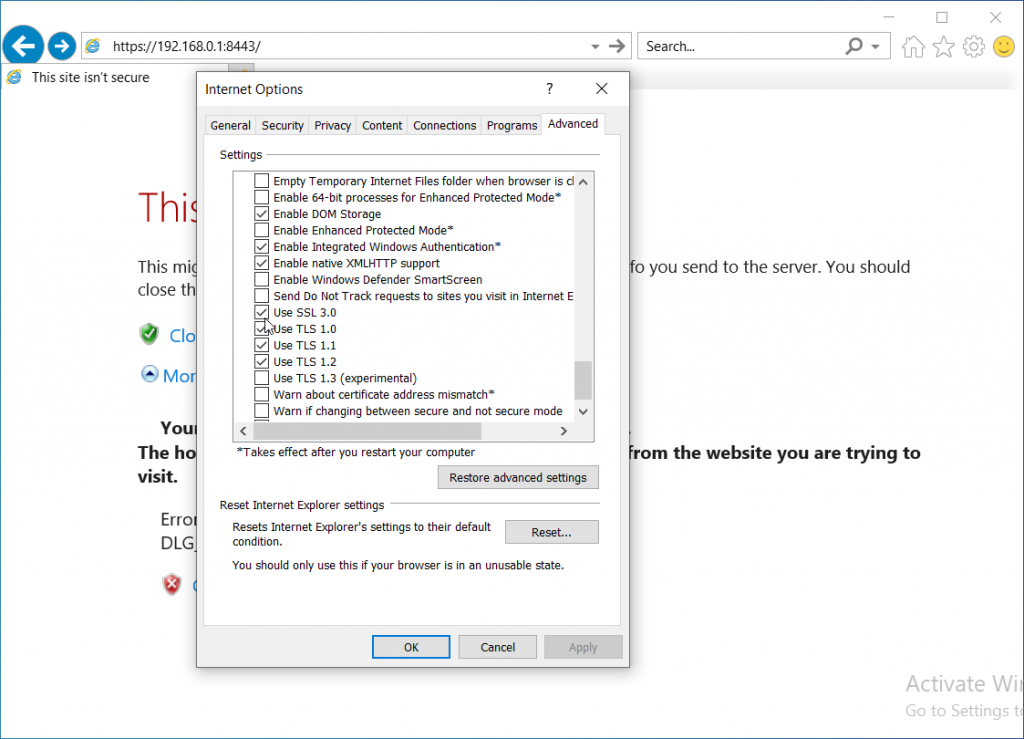
Generate Self signed certificate
Enable ssl in apache
sudo a2enmod ssl
Generate Cert
sudo openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout /etc/ssl/private/localhost.key -out /etc/ssl/certs/localhost.crt
Configure Apache
Edit the following config file
sudo vi /etc/apache2/sites-available/librenms.conf
Add the following
<VirtualHost *:443>
DocumentRoot /opt/librenms/html/
ServerName librenms.example.com
SSLEngine on
SSLCertificateFile /etc/ssl/certs/localhost.crt
SSLCertificateKeyFile /etc/ssl/private/localhost.key
CustomLog /opt/librenms/logs/access_log combined
ErrorLog /opt/librenms/logs/error_log
AllowEncodedSlashes NoDecode
<Directory "/opt/librenms/html/">
Require all granted
AllowOverride All
Options FollowSymLinks MultiViews
</Directory>
</VirtualHost>
Run the following commands
sudo a2ensite librenms.conf
sudo a2enmod rewrite
sudo systemctl restart apache2
Configure snmpd
sudo cp /opt/librenms/snmpd.conf.example /etc/snmp/snmpd.conf
Set the SNMP community string in the following file
sudo vi /etc/snmp/snmpd.conf
Then run these commands
sudo curl -o /usr/bin/distro https://raw.githubusercontent.com/librenms/librenms-agent/master/snmp/distro
sudo chmod +x /usr/bin/distro
sudo systemctl restart snmpd
Setup Crontab
sudo cp /opt/librenms/librenms.nonroot.cron /etc/cron.d/librenms
Copy logrotate config
sudo cp /opt/librenms/misc/librenms.logrotate /etc/logrotate.d/librenms
Set permissions
mkdir -p /opt/librenms/rrd /opt/librenms/logs
sudo chown -R librenms:librenms /opt/librenms
sudo setfacl -d -m g::rwx /opt/librenms/rrd /opt/librenms/logs
sudo setfacl -R -m g::rwx /opt/librenms/rrd /opt/librenms/logs
Web Installer
Restart apache
sudo systemctl restart apache2
Finish the install by going to
https://your-server/install.php
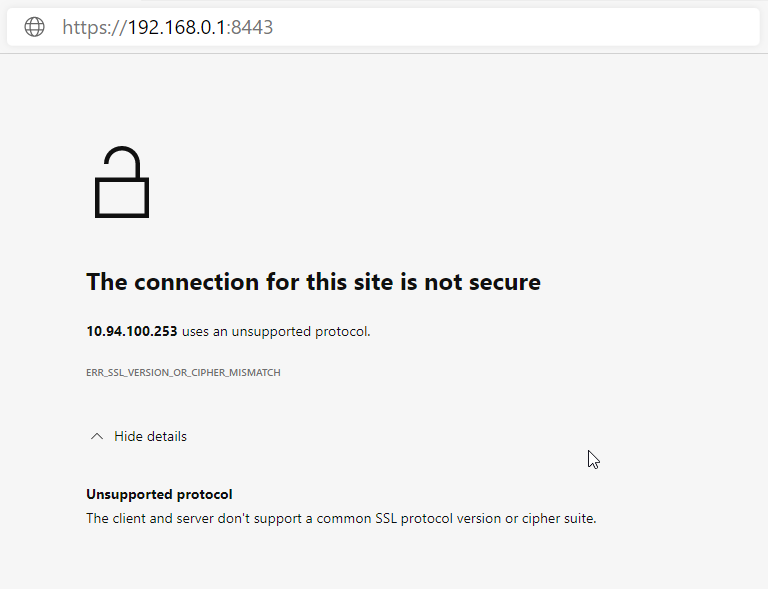
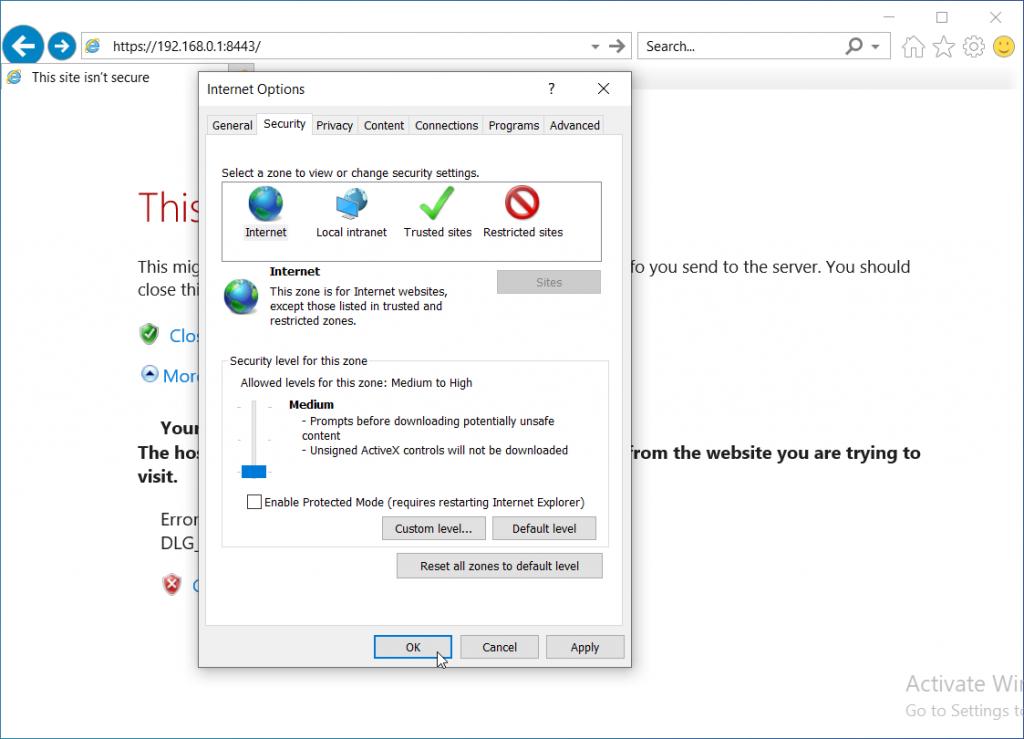
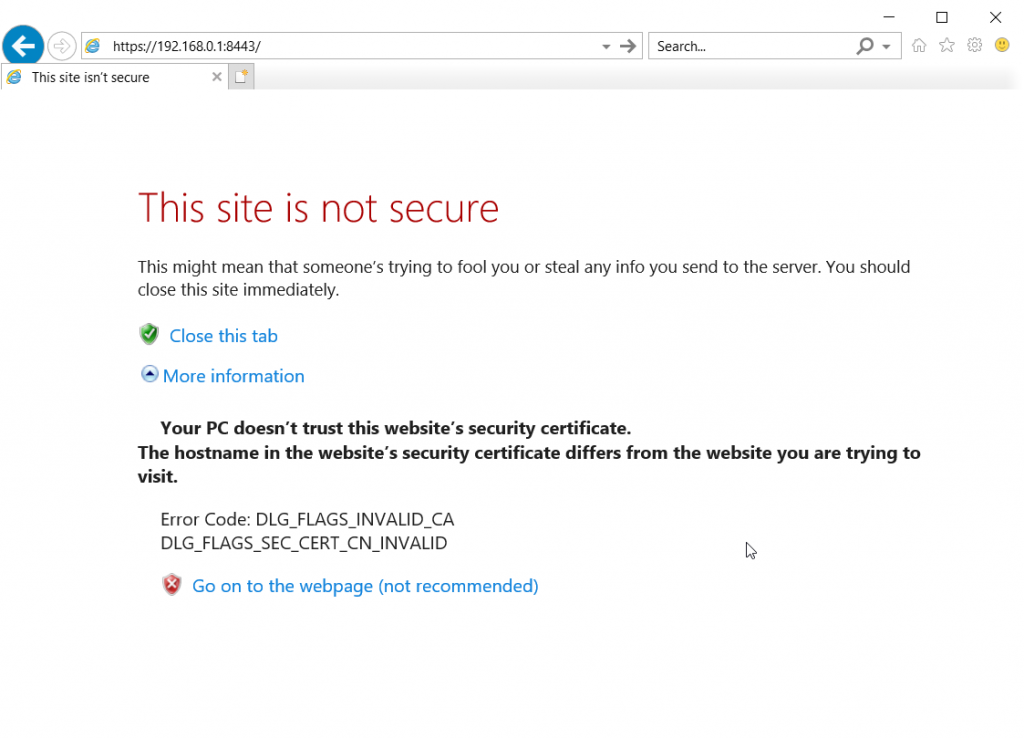
Change “your-server” to your server’s ip address, or hostname. Since we created a self signed certificate, you’ll need to accept the https error.
Validate
Back on the command line run the php validation script
sudo /opt/librenms/validate.php
Finally log into your new LibreNMS instance by going to
https://your-server
Change “your-server” to your server’s IP address or hostname.