Here are some notes on downgrading a Ubiquiti Airmax radio so it can run unsigned firmware.
Disclaimer, the following steps are potentially dangerous. Proceed with caution.
Ubiquiti introduced signed firmware around version 5.12. After that, you couldn’t flash unsigned firmware if a device already had signed firmware. You also couldn’t downgrade below 5.12.
Ubiquiti uses the update utility to enforce only flashing signed firmware. So what happens if you swap out the update utility with one from an unsigned firmware version?
This is the hack we’ll explore.
Here is a quick overview.
- Download firmware.
- Extract ubntbox out of the unsigned firmware.
- Move files (ubntbox, and unsigned firmware) to target radio.
- Modify
libevent versions in ubntbox to match the current signed firmware. Should only be needed if firmware version number is different.
- Upgrade! “Downgrade”…
Downloading firmware
You can download unsigned firmware from Ubiquiti. https://ui.com/download
Here is a link for the PowerBeam firmware. https://ui.com/download/software/nbe-m5-400
ℹ️Pro tip, you should be able to wget the firmware directly to a radio with wget http://dl.ubnt.com/firmwares/XW-fw/v5.6.15/XW.v5.6.15-sign.31612.170908.1440.bin
Note the http. No https. The wget version in older firmware has issues with SSL/TLS.
Extract ubntbox from the Unsigned Firmware
For this step we need binwalk.
sudo apt install binwalk
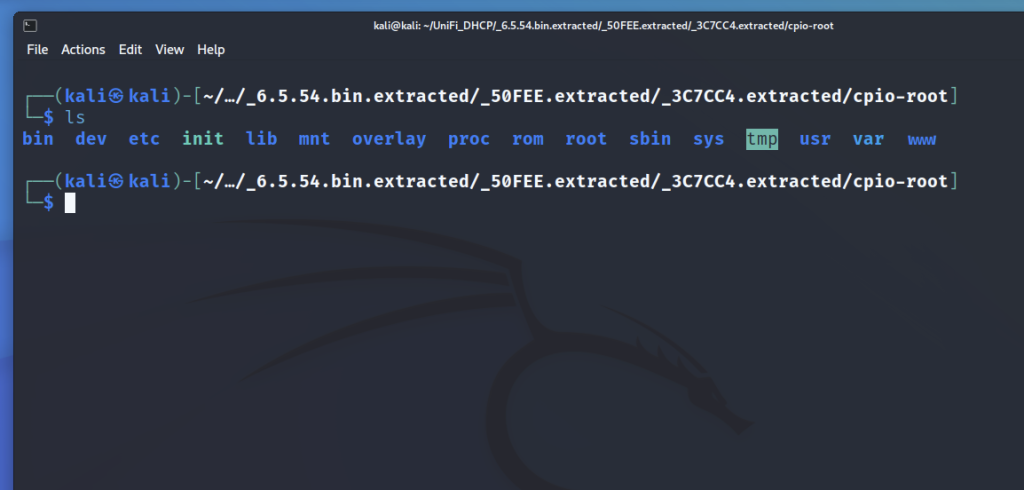
Next, extract the firmware with binwalk.
binwalk -e ./XW.v5.6.3.bin
It will extract the firmware to a folder named _XW.v5.6.3.28591.151130.1735.bin.extracted
We want the ubntbox binary which is at the following location.
_XW.v5.6.3.28591.151130.1735.bin.extracted/squashfs-root/bin/ubntbox
Move files (ubntbox, and unsigned firmware) to target radio
ℹ️scp and sftp most likely will not work. To get around this, you can set up a local web server like apache to serve the files, move the files into the /var/www/html directory and download to the radio with wget. You may not be able to download executable files. You can work around this by running chmod 644 ubntbox, download with wget, then chmod +x ubntbox to make it executable again.
On our computer, install and start the apache webserver
sudo apt install apache2
sudo systemctl start apache2
Next, copy ubntbox and firmware files to /var/www/html/. Replace the firmware name if different.
cp ./ubntbox /var/www/html/
cp ./XW.v5.6.3.bin /var/www/html/
On the radio, cd to the /tmp directory. Download ubntbox and the firmware from your computer. Change the IP address to your webserver IP.
wget http://192.168.1.2/ubntbox
wget http://192.168.1.2/XW.v5.6.3.bin
Rename firmware to fwupdate.bin
mv XW.v5.6.3.bin fwupdate.bin
Ensure ubntbox is executable.
chmod +x ubntbox
Upgrade “Downgrade” radio
We are ready to update the radio.
./ubntbox fwupdate.real -m
You may encounter the following error.
./ubntbox: can't load library 'libevent_core-2.0.so.5'
Since ubntbox is a dynamically linked binary, we may need to change the libevent library references to match the libevent libraries on the system. You can find the current libevent libraries with find / | grep libevent
Example output.
XW.v5.6.15-sign.31612.170908.1440# find / | grep libevent
/lib/libevent-2.1.so.6
/lib/libevent-2.1.so.6.0.2
/lib/libevent_core-2.1.so.6
/lib/libevent_core-2.1.so.6.0.2
/lib/libevent_extra-2.1.so.6
/lib/libevent_extra-2.1.so.6.0.2
/lib/libevent_openssl-2.1.so.6
/lib/libevent_openssl-2.1.so.6.0.2
Replace all libevent references in ubntbox with the correct versions on the current firmware.
You should now be able to downgrade to an unsigned firmware version.
A few interesting notes.
- /sbin is a link to /bin
- fwupdate is a simlink to fwupdate.real which is a link to ubntbox.
- ubntbox is like Busybox
- To download files, you may need to use wget over non https.