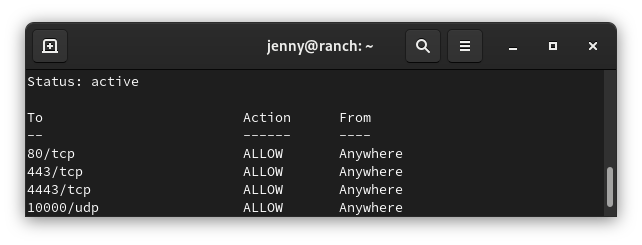
Here is a simple Ansible UFW firewall playbook.
You will need to install the Ansible collection community.general if it is not already installed.
ansible-galaxy collection install community.generalNext create the playbook. Modify the ports to your liking. Also remember you can put these variables in the Ansible inventory file so each hosts can have different settings.
---
- hosts: ubuntu
become: true
vars:
ssh_port: 22
http_port: 80
https_port: 443
tasks:
- name: Ensure UFW is installed
apt:
name: ufw
state: present
update_cache: yes
- name: Restrict SSH access to local IP addresses (RFC 1918)
block:
- name: Allow SSH from 10.0.0.0/8
community.general.ufw:
rule: allow
from_ip: 10.0.0.0/8
port: "{{ ssh_port }}"
proto: tcp
- name: Allow SSH from 172.16.0.0/12
community.general.ufw:
rule: allow
from_ip: 172.16.0.0/12
port: "{{ ssh_port }}"
proto: tcp
- name: Allow SSH from 192.168.0.0/16
community.general.ufw:
rule: allow
from_ip: 192.168.0.0/16
port: "{{ ssh_port }}"
proto: tcp
- name: Allow HTTPS access from the world
community.general.ufw:
rule: allow
port: "{{ https_port }}"
proto: tcp
- name: Allow HTTP access from the world
community.general.ufw:
rule: allow
port: "{{ http_port }}"
proto: tcp
- name: Enable UFW and set default policy to deny incoming
community.general.ufw:
state: enabled
policy: deny
Save the playbook as ubuntu_firewall.yaml
Run the playbook with:
ansible-playbook ubuntu_firewall.yaml -i inventory/hostsHere is a more advanced playbook that will loop through multiple IP addresses and ports.
---
- hosts: ubuntu
become: true
vars:
local_ports:
- { port: '22', proto: 'tcp' } # SSH
- { port: '161', proto: 'udp' } # SNMP
public_ports:
- { port: '80', proto: 'tcp' } # HTTP
- { port: '443', proto: 'tcp' } # HTTPS
local_ips:
- 10.0.0.0/8
- 172.16.0.0/12
- 192.168.0.0/16
tasks:
- name: Ensure UFW is installed
apt:
name: ufw
state: present
update_cache: yes
- name: Allow public_ports
community.general.ufw:
rule: allow
port: "{{ item.port }}"
proto: "{{ item.proto }}"
loop: "{{ public_ports }}"
- name: Allow access to local_ports from RFC 1918 local addresses
block:
- name: Allow local_ports from RFC 1918 local IPs
community.general.ufw:
rule: allow
from_ip: "{{ item.0 }} "
port: "{{ item.1.port }}"
proto: "{{ item.1.proto }}"
loop: "{{ local_ips | product(local_ports) | list }}"
- name: Enable UFW and set default policy to deny incoming
community.general.ufw:
state: enabled
policy: deny