Quick Summary: Operation Triangulation is an iOS zero-click exploit that will self destruct, looks to have been used since at least 2019, works on iOS 15.7, unsure if it works on iOS 16. Can collect location, mic recordings, photos, and manipulate iMessages. First point of entry is from an iMessage message, that compromises the device, after compromise, the message gets deleted.
https://securelist.com/operation-triangulation/109842/
Links for checking for infection.
https://securelist.com/find-the-triangulation-utility/109867/
https://github.com/KasperskyLab/triangle_check
The following is a list of C&C domains from the securelist.com article. Did a quick DNS lookup for each domain and they currently have the following records & IP addresses. Note that these can change at any time and some of the IP addresses are/can be shared with other legitimate websites if it is on a shared hosting provider.
addatamarket.net - sandy.ns.cloudflare.com, doug.ns.cloudflare.com - No A records, or TXT backuprabbit.com - nelci.ns.cloudflare.com, morgan.ns.cloudflare.com - No A records, or TXT businessvideonews.com - ns2.dnsowl.com, ns3.dnsowl.com, ns1.dnsowl.com - 198.251.81.30, 209.141.38.71, 107.161.23.204 cloudsponcer.com - Cloudflare, kipp.ns.cloudflare.com, joyce.ns.cloudflare.com datamarketplace.net - ns78.domaincontrol.com, ns77.domaincontrol.com, 34.98.99.30 mobilegamerstats.com - ns1.bitdomain.biz, No A records, TXT=v=spf1 redirect=_spf.mailhostbox.com snoweeanalytics.com - cody.ns.cloudflare.com, arlee.ns.cloudflare.com - 104.21.76.6, 172.67.184.201 tagclick-cdn.com - ns4.bitdomain.biz, ns3.bitdomain.biz, ns2.bitdomain.biz, ns1.bitdomain.biz - No A records, TXT=v=spf1 redirect=_spf.mailhostbox.com" topographyupdates.com - nero.ns.cloudflare.com, dalary.ns.cloudflare.com - 104.21.27.67, 172.67.141.199 unlimitedteacup.com - nelci.ns.cloudflare.com, javon.ns.cloudflare.com - 104.21.55.58, 172.67.145.72 virtuallaughing.com - elaine.ns.cloudflare.com, braden.ns.cloudflare.com - 104.21.60.240, 172.67.202.140 web-trackers.com - dns1.registrar-servers.com, dns2.registrar-servers.com - 15.164.228.250 growthtransport.com - ns3.dnsowl.com, ns2.dnsowl.com, ns1.dnsowl.com - 198.251.81.30, 107.161.23.204, 209.141.38.71 anstv.net - ns64.domaincontrol.com, ns63.domaincontrol.com. - 93.90.223.185 ans7tv.net - ns37.domaincontrol.com,ns37.domaincontrol.com - 93.90.223.185
List of domains
addatamarket.net backuprabbit.com businessvideonews.com cloudsponcer.com datamarketplace.net mobilegamerstats.com snoweeanalytics.com tagclick-cdn.com topographyupdates.com unlimitedteacup.com virtuallaughing.com web-trackers.com growthtransport.com anstv.net ans7tv.net
List of IPv4 addresses used
107.161.23.204 198.251.81.30 209.141.38.71 34.98.99.30 172.67.184.201 104.21.76.6 172.67.141.199 104.21.27.67 172.67.145.72 104.21.55.58 104.21.60.240 172.67.202.140 15.164.228.250 209.141.38.71 198.251.81.30 93.90.223.185
Bash command to get an updated IP address list. bad.txt contains all the above domain names.
for i in `cat bad.txt` ; do dig $i a +short >> badips.lst; doneCheck DNS logs
If you have a DNS server, you can check to see if there has been any name resolution by using the following. Change named.log to your dns log
# list=""addatamarket.net" "backuprabbit.com" "businessvideonews.com" "cloudsponcer.com" "datamarketplace.net" "mobilegamerstats.com" "snoweeanalytics.com" "tagclick-cdn.com" "topographyupdates.com" "unlimitedteacup.com" "virtuallaughing.com" "web-trackers.com" "growthtransport.com" "anstv.net" "ans7tv.net"" # for domain in $list; do echo $domain && sudo grep -i $domain /var/log/named.log; done
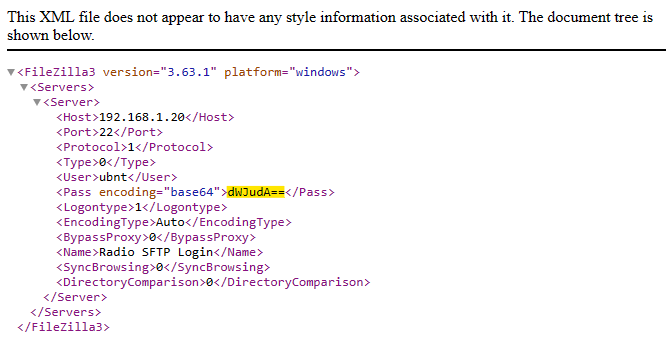
Setup Mikrotik capture traffic
Mikrotik packet sniffer settings to capture traffic coming or going to the above IP addresses.
/tool sniffer
set file-limit=32000KiB file-name=Triangulation filter-ip-address="107.161.23.20\
4/32,198.251.81.30/32,209.141.38.71/32,34.98.99.30/32,172.67.184.201/32,104.\
21.76.6/32,172.67.141.199/32,104.21.27.67/32,172.67.145.72/32,104.21.55.58/3\
2,104.21.60.240/32,172.67.202.140/32,15.164.228.250/32,209.141.38.71/32,198.\
251.81.30/32,93.90.223.185/32"
You can then start the sniffer by running Tools -> Packet Sniffer Settings -> Start
or run
/tool/sniffer/start
Resolution
Apple issued an update that fixes the kernel part of the vulnerability.
https://securelist.com/triangledb-triangulation-implant/110050/