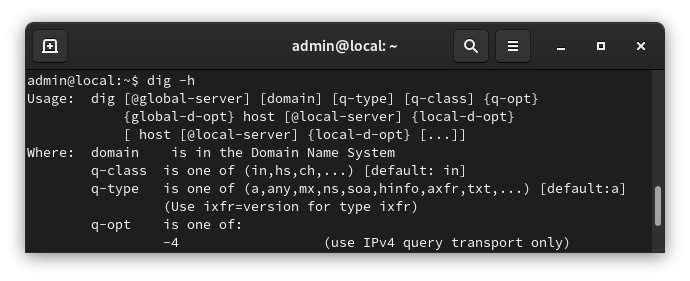
Dig is a DNS lookup utility. It is included in most Linux distributions by default, but if it isn’t you can easily install dig with the following command.
The dig utility is apart of the dnsutils package
sudo apt-get install dnsutils -y
After it is installed, we can verify that it is working with
dig -v
For more information on how to use dig, refer to the following link.
https://www.howtogeek.com/663056/how-to-use-the-dig-command-on-linux/
The following is copied and pasted from the dig man page.
NAME
dig - DNS lookup utility
SYNOPSIS
dig [@server] [-b address] [-c class] [-f filename] [-k filename] [-m] [-p port#] [-q name]
[-t type] [-v] [-x addr] [-y [hmac:]name:key] [[-4] | [-6]] [name] [type] [class]
[queryopt...]
dig [-h]
dig [global-queryopt...] [query...]
DESCRIPTION
dig is a flexible tool for interrogating DNS name servers. It performs DNS lookups and
displays the answers that are returned from the name server(s) that were queried. Most DNS
administrators use dig to troubleshoot DNS problems because of its flexibility, ease of use
and clarity of output. Other lookup tools tend to have less functionality than dig.
Although dig is normally used with command-line arguments, it also has a batch mode of
operation for reading lookup requests from a file. A brief summary of its command-line
arguments and options is printed when the -h option is given. Unlike earlier versions, the
BIND 9 implementation of dig allows multiple lookups to be issued from the command line.
Unless it is told to query a specific name server, dig will try each of the servers listed
in /etc/resolv.conf. If no usable server addresses are found, dig will send the query to the
local host.
When no command line arguments or options are given, dig will perform an NS query for "."
(the root).
It is possible to set per-user defaults for dig via ${HOME}/.digrc. This file is read and
any options in it are applied before the command line arguments. The -r option disables this
feature, for scripts that need predictable behaviour.
The IN and CH class names overlap with the IN and CH top level domain names. Either use the
-t and -c options to specify the type and class, use the -q the specify the domain name, or
use "IN." and "CH." when looking up these top level domains.
SIMPLE USAGE
A typical invocation of dig looks like:
dig @server name type
where:
server
is the name or IP address of the name server to query. This can be an IPv4 address in
dotted-decimal notation or an IPv6 address in colon-delimited notation. When the
supplied server argument is a hostname, dig resolves that name before querying that name
server.
If no server argument is provided, dig consults /etc/resolv.conf; if an address is found
there, it queries the name server at that address. If either of the -4 or -6 options are
in use, then only addresses for the corresponding transport will be tried. If no usable
addresses are found, dig will send the query to the local host. The reply from the name
server that responds is displayed.
name
is the name of the resource record that is to be looked up.
type
indicates what type of query is required — ANY, A, MX, SIG, etc. type can be any valid
query type. If no type argument is supplied, dig will perform a lookup for an A record.